![FALSE] Will the visit records in 'LeaveHomeSafe' mobile app be kept for 7 years if submitted to the government? - HKBU FactCheck Service FALSE] Will the visit records in 'LeaveHomeSafe' mobile app be kept for 7 years if submitted to the government? - HKBU FactCheck Service](https://comd.hkbu.edu.hk/factcheckservice/wp-content/uploads/2021/03/leave-home-safe.png)
FALSE] Will the visit records in 'LeaveHomeSafe' mobile app be kept for 7 years if submitted to the government? - HKBU FactCheck Service
Anonymising personal data 'not enough to protect privacy', shows new study | Imperial News | Imperial College London

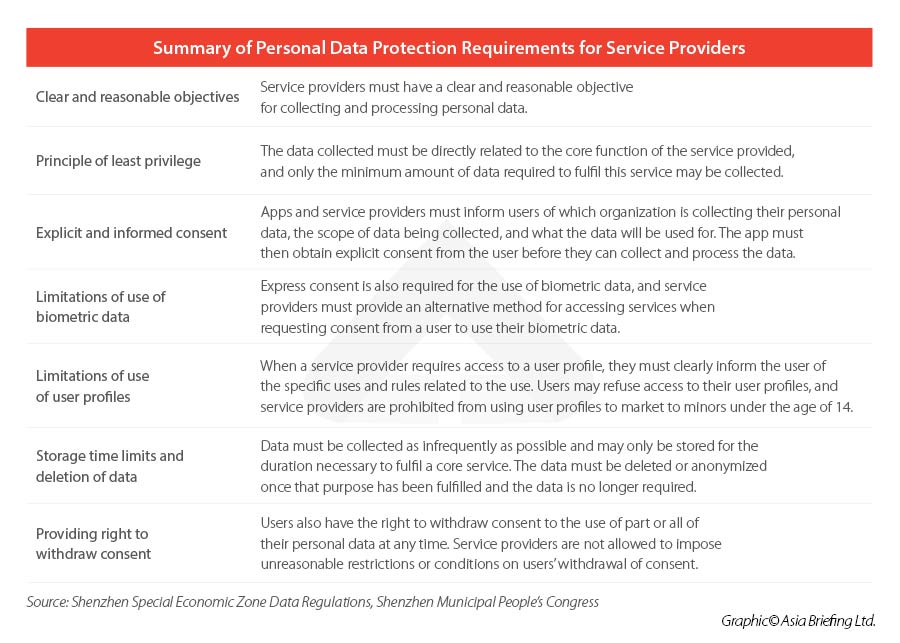
What does 'data protection by design and by default' mean under EU Data Protection Law? | by Golden Data Law | Golden Data | Medium
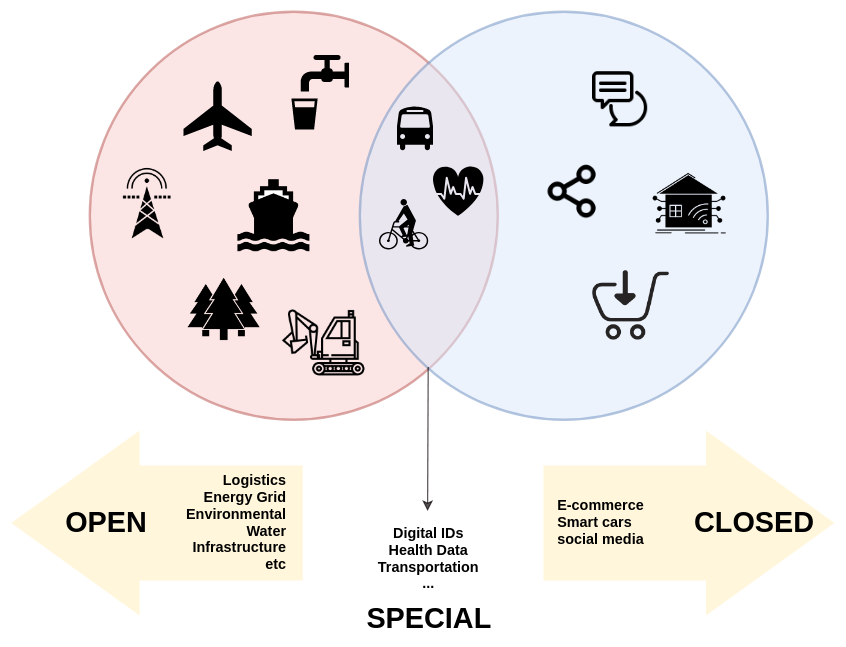
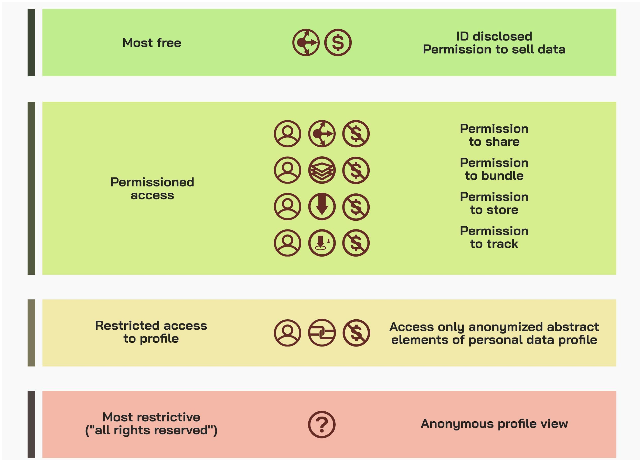
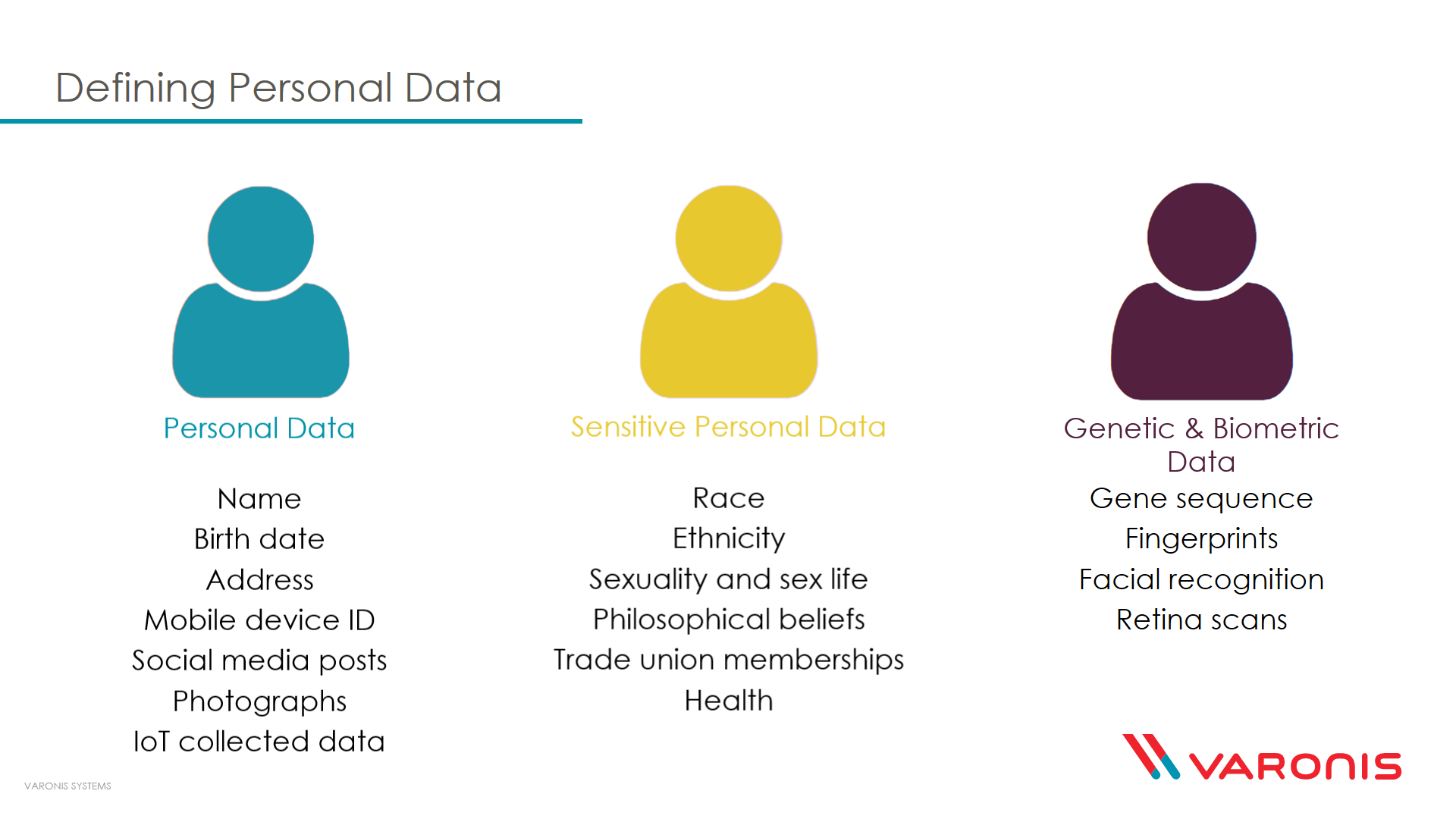
Thoughts on personal data vs non-personal data | by Yasodara Cordova | Berkman Klein Center Collection | Medium